Any of us could fall victim to cyberattacks – how to protect ourselves? Part 1
On average, around 30 000 websites are hacked around the world every day. Even in Estonia, the computer systems and websites of various state institutions, companies, and private persons fall victim to attacks perpetrated by cybercriminals on a daily basis. How can we protect ourselves these attacks?
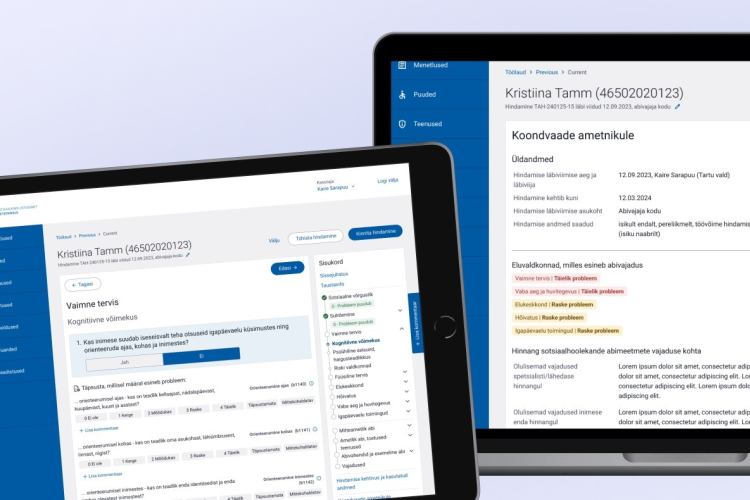
We conducted an interview on the subject of cyberattacks with developers at Trinidad Wiseman who have over 10 years of work experience with the most popular content management systems, Drupal and WordPress.
Many people simply set their platform of choice up but either due to ignorance or a wish to cut costs, they do not update it regularly. In this article, we will talk about why someone might perpetrate cyberattacks, what the potential consequences of that may be, and we will also provide some suggestions on how you can protect yourself from all of it.
Who and why should attack my web?
Unfortunately, the real question today is no longer whether someone can possibly hack your web, but when they will do so. No one is 100% safe, not even giants like Google or Intel. Why is that?
Technology is evolving incredibly fast, which means that it is highly likely that before any new updates are released, vulnerabilities may appear, which hackers can then skillfully make use of for their own ends.
There are many options for conducting an attack – for example, someone may track your activities via malware they have previously sent to you via e-mail, or they may try to exploit weaknesses on your website.
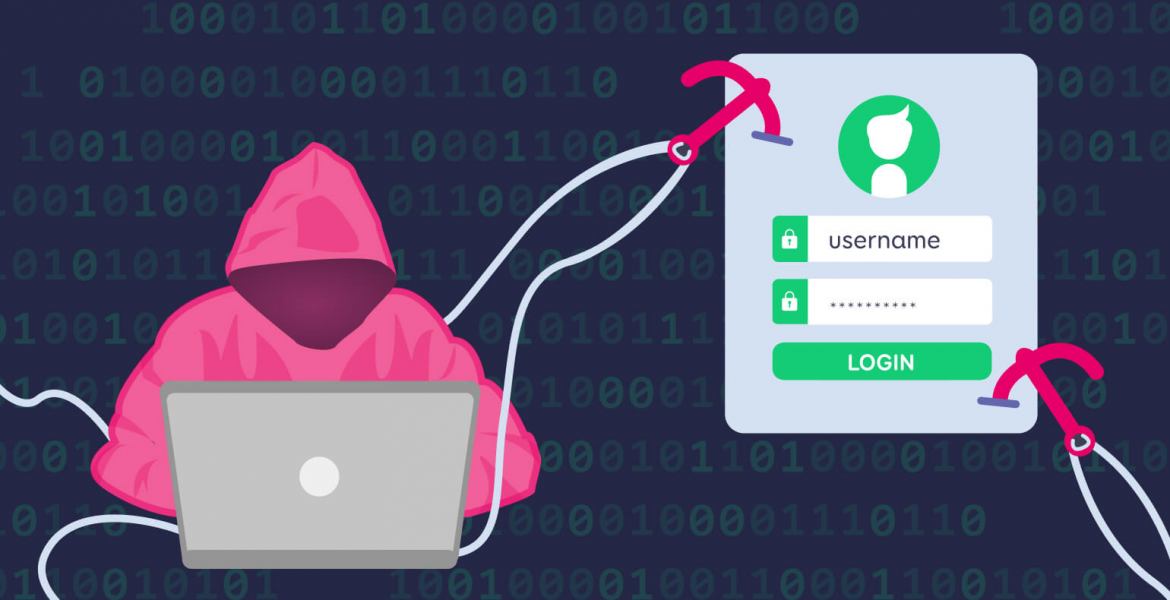
Most of the time, no one’s website or online store is attacked on purpose. Cybercriminals use automated systems: robots are provided a lot of public websites to scan and a lot of erroneous code and problematic plugins (e.g. ones that provide access to credit card details or the personal data of customers, ones that lack preventative security etc.) to identify.
The main motives behind cyberattacks:
- lucrative interests – the goal is to gather the personal data of customers or their usernames and passwords; in the case of online stores, payment data is phished for. It is also possible to redirect trusting customers to another environment via the online store with the goal of stealing their data.
- attacking marketing via SEO – all articles on a given website are filled with the hacker’s own links. For example, the cybercriminal can make it seem like everything is fine on your website, but the Google Search Engine may actually be directing people elsewhere.
- defacing – this is essentially electronic graffiti, where cyber vandals replace the content of a website with their own message. Usually, the message is political or religious and may include disturbing imagery.
- in rarer cases, a specific person or company may be chosen as the target of the attack. In this case, a piece of malware may be sent to an owner or developer of the company ahead of time, e.g. via e-mail, and once the recipient accesses their server or logs into the admin dashboard on their computer, then the perpetrator will get the information they are looking for.

How do I know that my website has been attacked?
Attacking and hacking a website are completely different situations. During an attack, you can still protect your website by increasing its security levels. In this section, we will be taking a closer look at how you can tell which one your website or system has fallen victim to.
To conduct an automated security scan of your website, you can use various options from plugins and your website host’s tools to separate third-party services. Some free foreign services are also available, such as the free software for Drupal and WordPress, which can be found on Sucuri.
We recommend that you log your system’s activities, which can help in quickly identifying (even internally) who and when has made changes to your website (e.g. edited or deleted something). You should definitely monitor these logs periodically.
By monitoring logs, we can see whether anyone has tried to access the website via unusual methods. If this has occurred, then it can usually be traced to an IP address which can be used to identify what exactly was attempted to do. It is also recommended that you add the IP address to a blacklist for a while.
If suspicious activity increases, then you can use monitoring software to set up e-mail notifications for them. It is important to note that automated attacks conducted by bots may last for weeks and take place in waves, so that they may be active for a while (500-600 incoming queries), calm down, and then start up again after some time has passed.
If someone has already hacked into your website, then the site admin may not notice anything out of the ordinary, but if you check the website on a different device, it may start to seem suspicious (e.g. advertorial texts may be interwoven with other text on the blog and these may redirect users to spam pages).
You may also receive feedback from your clients that something is wrong. It is not unusual for the first e-mail notification to come from an accommodation provider or from CERT.EE, the Information System Authority’s security incident management organisation.
In bigger companies, a separate so-called security detective has often been employed to chase down leads in order to figure out when and how an attack took place, if and what kind of information they accessed etc.
What kind of consequences and damages can an intrusion cause?
That depends on how big the cyberattack was and on what type of website it was carried out on or in other words, what kind of data can be leaked from the website.
The one thing you can be sure of is the fact that it always takes time and money to deal with the consequences of both small and large intrusions.
There are various different kinds of damage scenarios – starting with the ruin of the company’s reputation, data chaos, and the service being blocked to dropping stock prices.
Customer e-mail addresses may be added to spam lists, employees working on higher positions may be targeted with phishing e-mails to get other information from them.
For example, in the case of an online store, credit card details may be collected and used across the world. Another thing to take into consideration in the case of online stores is that if your customers’ data is sensitive, then you must also account for having to hire a lawyer and you must be prepared for potential fines.
You must also inform AKI (the Data Protection Inspectorate) and all of your customers. It is also recommended to open up an information hotline or find a contact person who can answer any questions your customers may have.
On the other hand, if the website that has fallen victim to an attack is a blog for example, then the damages are likely a lot smaller.
What to do when there has already been an intrusion?
First, you must establish what kind of hacking took place – where exactly did the attackers gain access to and what did they do, did they gain access to the administrative side or did they take advantage of a vulnerability on your website (e.g. Cross Site Scripting or an SQL Injection) and gain access that way.
Sometimes, you can come up against well thought-out cybercrime, where an online store is hijacked AKA the store manager’s business is halted and a ransom is demanded in exchange for return of control.
If the attackers have obtained your customers’ data, then we recommend doing the following:
- contact the Data Protection Inspectorate (they will provide you with exact instructions on what to do and how to inform your customers)
- contact your developers
- contact your server admin
- you may also contact CERT (they monitor Estonian domains)
- inform your customers and open an information hotline to ensure that your customers can get answers to any questions they may have
What should a developer do if a website has been hacked? Most of the time, they have two options:
- we recommend restoring the website from a backup that was created prior to the attack. This is the fastest and cheapest option.
- if you do not have a backup (that is old enough), then you must start cleaning the page manually. This may be very time-consuming and in the worst case, the malware may remain hidden somewhere. If the website is a simpler one, then it may be worth considering reinstalling the website again from the source code and re-entering the content.
Can hackers be caught and punished?
World-class hackers are generally true professionals who work as subcontractors and who are extremely difficult if not impossible to catch.
Identifying a hacker requires years of serious detective work and unfortunately, it is not done in Estonia. There is a much higher likelihood of catching amateur or careless cybercriminals who do not know how to cover up their tracks.
If you are interested in reading more on the subject, then we recommend checking out stories on the Darknet Diaries, which contain examples of fateful mistakes that hackers have made.
We hope that this first part of the article provided you with new information about the main motives and methods behind cyberattacks and that you gained some new ideas on how to monitor for attacks and how to identify whether your website has already been hacked.
Next week, we will provide recommendations on how to protect your website and prevent any intrusions ahead of time in the second part of this article.